A Complete Guide to Understanding This IP Address
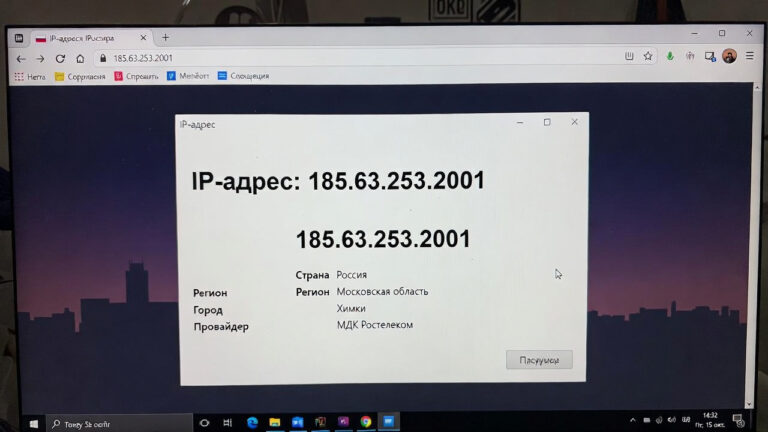
In the digital world, numbers often tell stories. One such number sequence that catches attention is 185.63.253.2001. At first glance, it looks like a standard IP address, but many users stumble upon it while checking server logs, firewall alerts, analytics data, or security tools. This naturally raises questions: What is it? Where does it come from? Is it safe?
This article breaks everything down in a clear, beginner-friendly way. Whether you’re a website owner, developer, cybersecurity enthusiast, or simply curious, this guide will help you understand what’s going on behind the scenes.
Understanding IP Addresses in Simple Terms
An IP address is like a digital home address. Every device connected to the internet uses one to send and receive data. Without IP addresses, the internet wouldn’t function.
There are two major versions in use today:
-
IPv4 – Uses numeric values separated by dots
-
IPv6 – Uses longer alphanumeric strings
Most people still encounter IPv4 addresses more often, especially when reviewing logs or server activity.
Is 185.63.253.2001 a Valid IP Address?
This is an important question.
A standard IPv4 address consists of four numbers, each ranging from 0 to 255. The structure looks like this:
Now here’s the catch:
The final segment in 185.63.253.2001 exceeds the valid range. Because of this, it does not follow standard IPv4 formatting rules.
What does this mean?
-
It may be a typo or formatting error
-
It could be logged incorrectly by software
-
It might represent a port-appended value
-
It may be used internally by custom systems
This alone explains why so many people search for it.
Why Do People See This IP in Logs or Tools?
There are several realistic scenarios where this number shows up:
1. Combined IP and Port Representation
Some systems accidentally combine an IP address and a port number into one string. For example:
When formatting breaks, it may appear merged.
2. Software Parsing Errors
Improperly configured firewalls, proxies, or analytics tools sometimes misinterpret traffic data.
3. Internal Network Labeling
Private systems or testing environments may use non-standard formats for identification.
4. Bot or Script Activity
Automated scripts can generate malformed request headers, causing odd entries in server logs.
Common Situations Where This Appears
You’re more likely to encounter this address in:
-
Website access logs
-
Firewall alerts
-
Hosting provider reports
-
Security plugins
-
API request records
-
Network monitoring dashboards
Seeing it once isn’t necessarily a red flag. Context matters.
Is 185.63.253.2001 Dangerous?
Short answer: not automatically.
Because this is not a standard public IP, it’s unlikely to directly represent a real device on the internet. However, what triggers its appearance may still deserve attention.
When you should investigate:
-
Repeated requests in a short time
-
Failed login attempts
-
API abuse patterns
-
High traffic spikes
-
Requests to sensitive endpoints
When it’s usually harmless:
-
Single log entry
-
No suspicious behavior
-
No server performance impact
-
No security alerts triggered
How to Investigate Unknown IP Entries Safely
If you notice unusual IP-like values in your logs, follow these steps:
Step 1: Check the Raw Log Format
Look for extra characters like colons or spaces that may indicate formatting issues.
Step 2: Inspect Request Headers
Malformed headers can reveal whether it’s a bot, crawler, or broken client.
Step 3: Review Access Frequency
One-time access is usually harmless. Repetition may need action.
Step 4: Use Monitoring Tools
Security plugins, SIEM tools, and firewalls can help categorize traffic.
IP Addresses and Cybersecurity Awareness
Understanding unusual IP entries improves your overall security posture. Many attacks don’t start loudly; they begin as small anomalies.
Learning how to read and interpret IP data helps you:
-
Detect early threats
-
Reduce false positives
-
Improve server performance
-
Strengthen firewall rules
Can You Trace 185.63.253.2001?
Because the value doesn’t meet IPv4 standards, traditional IP lookup tools won’t return accurate results.
If you’re trying to trace traffic:
-
Extract the first four valid octets
-
Check for appended ports
-
Review timestamps
-
Compare with known IP ranges
Always rely on multiple data points instead of a single log line.
IPv4 vs IPv6: Why Confusion Happens
The internet is in a transition phase. IPv6 exists because IPv4 addresses are limited. This overlap sometimes creates confusion in logging systems, especially older software.
Some systems:
-
Misread IPv6-mapped IPv4 addresses
-
Fail to sanitize input properly
-
Log partial or malformed addresses
This explains many unusual IP-related searches online.
Best Practices for Website Owners
If you manage a website or server, here’s how to stay safe and organized:
-
Keep server software updated
-
Use trusted firewall rules
-
Enable rate limiting
-
Monitor access logs weekly
-
Don’t panic over single anomalies
Proactive monitoring beats reactive cleanup every time.
SEO Perspective: Why This Keyword Gets Traffic
Technical keywords like 185.63.253.2001 attract users because:
-
People copy-paste directly from logs
-
Curiosity triggers quick searches
-
Security concerns create urgency
-
There’s little clear documentation online
Creating helpful content around such terms improves trust and organic visibility.
Common Myths About Strange IP Addresses
Myth 1: Every unknown IP is a hacker
Reality: Most are bots, crawlers, or errors
Myth 2: One suspicious entry means compromise
Reality: Attacks show patterns, not single lines
Myth 3: Blocking everything is safest
Reality: Over-blocking can break legitimate services
Final Thoughts
The keyword 185.63.253.2001 may look alarming at first, but in most cases, it’s a non-standard or misformatted IP entry rather than a direct threat. Understanding how IP addresses work — and how systems sometimes log them incorrectly — removes fear and replaces it with clarity.
If you encounter this value, focus on behavior, patterns, and context, not just the number itself. Knowledge is your strongest security tool.